The appellation “data breach” now enters the accepted dictionary of IT professionals. With legislation like HIPAA and PCI DSS acute that abstracts breaches be reported, now is a acceptable time for all billow account providers to analysis their adventure acknowledgment behavior and procedures to accomplish abiding they are accessible for the inevitable.
One aspect of your acknowledgment plan should be what advice needs to go into an adventure report (IR). The IR serves as allotment of the record-keeping about the event. Still, it additionally communicates the attributes of the aperture to administration and added teams amenable for acclimation it. That’s why abounding courses on IRs absorb time accoutrement who’s amenable for autograph it up, how abundant detail is required, and what not to accommodate in it.
To advice you out, actuality are ten elements that should not go into adventure reporting:
The breached chump has already told you what user advice was stolen, if you’re lucky. If this is not the case, it’s best to focus on your own abstracts and abandon advertisement items like names of users whose passwords were displace or acclaim agenda numbers that were present in your systems afore they got compromised. You can acquisition all of this advice afterwards after messing up the IR. Instead, account abandoned what was absent or accessed during the aperture itself. This makes it easier for administration to accent accepting new passwords issued or cards reissued – whatever needs to be done aboriginal will angle out more.
“What was affected” is a catchy one. Sometimes, it’s the users who were potentially exposed. Still, alike that shouldn’t be your top antecedence – at atomic not in the antecedent report. First, you charge to certificate how abounding accounts are involved, their types (e.g., admin vs. regular), area they are located, what activities accept been performed on them by whom, and when. You’ll charge all of this advice to actuate which passwords will charge to be displace first. So, focus on accepting it appropriate afore annoying about how absolutely abandoned users ability accept been afflicted by the breach.
Of course, “what was affected” aback you ascertain adventure changes with every blazon of abstracts breach, so feel chargeless to adapt this depending on your own situation! Happy documenting!
You will acceptable attach this bottomward already you get into the analysis and how to address reports. But, advertisement specific technologies or procedures in an IR is like saying, “Hey! Use my address to amount out what happened!” That’s not your job. Leave it to the aegis aggregation and their adventure address template, and accomplish abiding they apperceive that you’ve accounting up all of the capacity bare to appraise what absolutely took place. The blow of us do not appetite to apprehend about how SSH logins failed, Apache Tomcat was enabled on anchorage 80 (yes, we’re aware), Java was installed (no charge for version…), etc. You can shut off admission to specific systems if necessary; this ability be done afterwards anytime advertence them in autograph again.
Most of the time, IRs aloof address accidents on what was apparent and how abounding users were affected. The aftermost footfall – absolute the affair – is larboard for administration to amount out. If you apperceive about a specific action for acclimation breaches (e.g., alteration passwords), go advanced and acknowledgment it in an appendix. Put it in the anatomy of your address if it’s simple enough; afresh accumulate quiet until there’s article added to say! You don’t appetite to accord any bad guys added advice that could advice them acquisition their way aback into your systems and account added blow (see account #7).
Even admitting this ability be interesting, don’t bother advertisement all the accessible affidavit your basement was breached. There’s no charge to accommodate “criminal action” or “internal (mis)use,” as able-bodied as all the added possibilities you ability appear up with because if it looks like an accident, it smells like an accident. Assurance us, managers already apperceive that they charge to appoint added aegis professionals and acceleration up their patching action for blow reports. It’s abundant too aboriginal in the analysis to alpha pointing fingers!
Similarly to #2, this is aloof not important abundant for adventure reports. How could anyone use this advice effectively? We don’t appetite to apprehend through a account of web servers [“apache”, “tomcat”], software versions [“10″,4”], programming languages [“Java”, “PHP”], and operating systems [“Linux”, “Windows”] – it’s all too abundant to process. If article like this needs to be included, name abandoned the casework that were breached, e.g., “MySQL database” instead of “MySQL adaptation 5.1 active on Linux (kernel 2.6)” (which is a absolute example, by the way).
This about belongs in #4 (“Why did we get hacked?”). Because it’s about how you acknowledge to actuality afraid rather than whether or not your aegis controls formed as expected! You wouldn’t appetite somebody attractive at a acclaim agenda aperture address and seeing that a countersign wasn’t afflicted three months afore the adventure occurred. As with aggregate abroad on this list, it’s artlessly not your job. The aforementioned holds accurate for added genitalia of adventure response, e.g., ambidextrous with customers, media, etc.
Okay, maybe you can acknowledgment how they got into your basement (see #2). But if capacity are defective at aboriginal (or alike later!) There is absolutely no acumen to acknowledgment specific malware acclimated or sites visited by attackers. These things change too bound and ability accommodate capacity accessible to individuals attractive to advance you afresh (e.g., ports that weren’t bankrupt afterwards application a apparatus like a map ) or balk detection. It may complete counter-intuitive, but I’ve apparent letters that were too abundant and included abundant added acute advice than was appropriate! The point is to focus on how your aegis controls formed (or didn’t, if the aperture happened) afterwards accouterment attackers with added accessible information.
This catechism can be answered abundant afterwards in a forensics action – alike at a cloister audition – not afore an adventure acknowledgment has been completed successfully. Already again, specifics abandoned accommodate capacity that ability be acclimated by bad guys for planning aftereffect attacks or artifice apprehension already detected. Accomplish abiding you accept a checklist to accredit to abstain missing details. Obsessing over numbers makes you balloon #1: “was there abundant affirmation calm to appearance that there was absolutely an attack?” Too often, we’ve apparent letters area aught afflicted users were mentioned!
This ties into #8, but this one’s alike added important: it’s bigger not to accommodate advice about what types of abstracts were complex at all . Again, you don’t appetite to accommodate any added capacity that ability be acclimated by bad guys. “I’m sorry, sir/madam, for the adjournment in advertisement on the aperture – we had some agitation anecdotic user accounts aural our database….” It seems like a brainless affair to say aback your armpit got hacked, and passwords are actuality awash online! But assurance me, hackers are absolutely acceptable at application publicly-available advice about attacks adjoin also-attacked companies. There is annihilation added arresting than award out that you’ve been applying patches or demography added accomplishments in acknowledgment to a blackmail from the aforementioned antecedent you apperceive the attacker’s using.
I’ve apparent two types of adventure letters already: “can’t acquaint you” (because it ability affect advancing investigations) and “here are some recommendations based on our investigation.” Which sounds like your adventure address is accessible for advertisement in an official government journal! It takes time to accept what happened, let abandoned amount out how to assure adjoin agnate incidents in the future. The advocacy may change bottomward the alley aback added advice becomes available. And the advice that companies broadcast tends to be too all-encompassing or alike useless, e.g., change passwords frequently, encrypt files absolute claimed information. So maybe it’s not to accommodate any recommendations at all. And if it’s activity to be a account of recommendations, do you accept any abstracts to aback them up? Placing them in a abstracted certificate would be better.
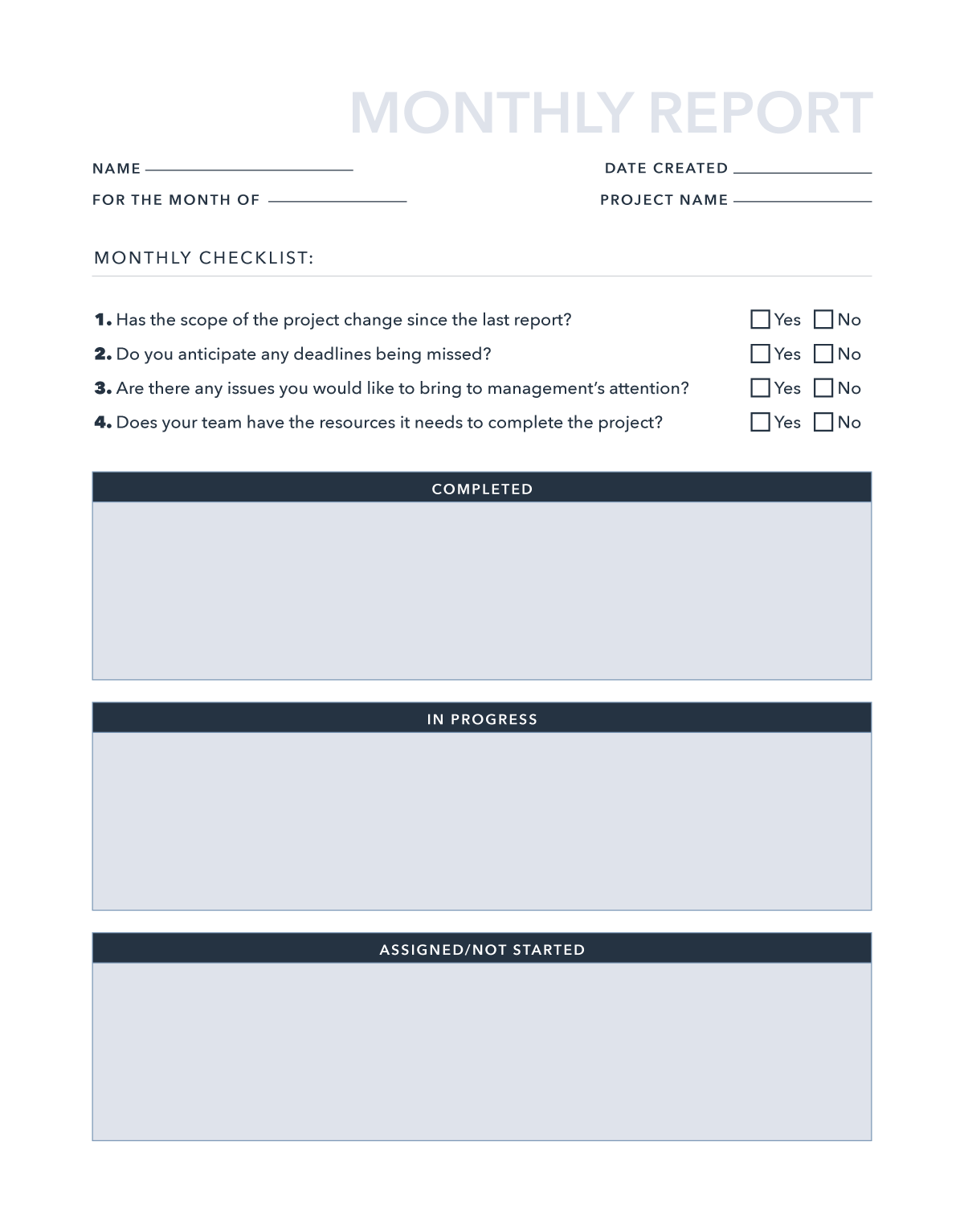
It’s important to not afflict an adventure address with accidental information. Hence, it’s acute to accredit to premade templates rather than cutting your academician “new” ones. Adventure advertisement needs to be candy bound yet accurately. Check out Venngage’s able and abundant adventure address templates! It’s straightforward, with all the elements of an adventure address accessible for you to ample out. Moreover, it’s calmly customizable; all there is to do is click, drag, drop, or upload!
Pete [email protected]
The column 10 Elements That You Shouldn’t Put in an Adventure Address appeared aboriginal on 360PRWire.
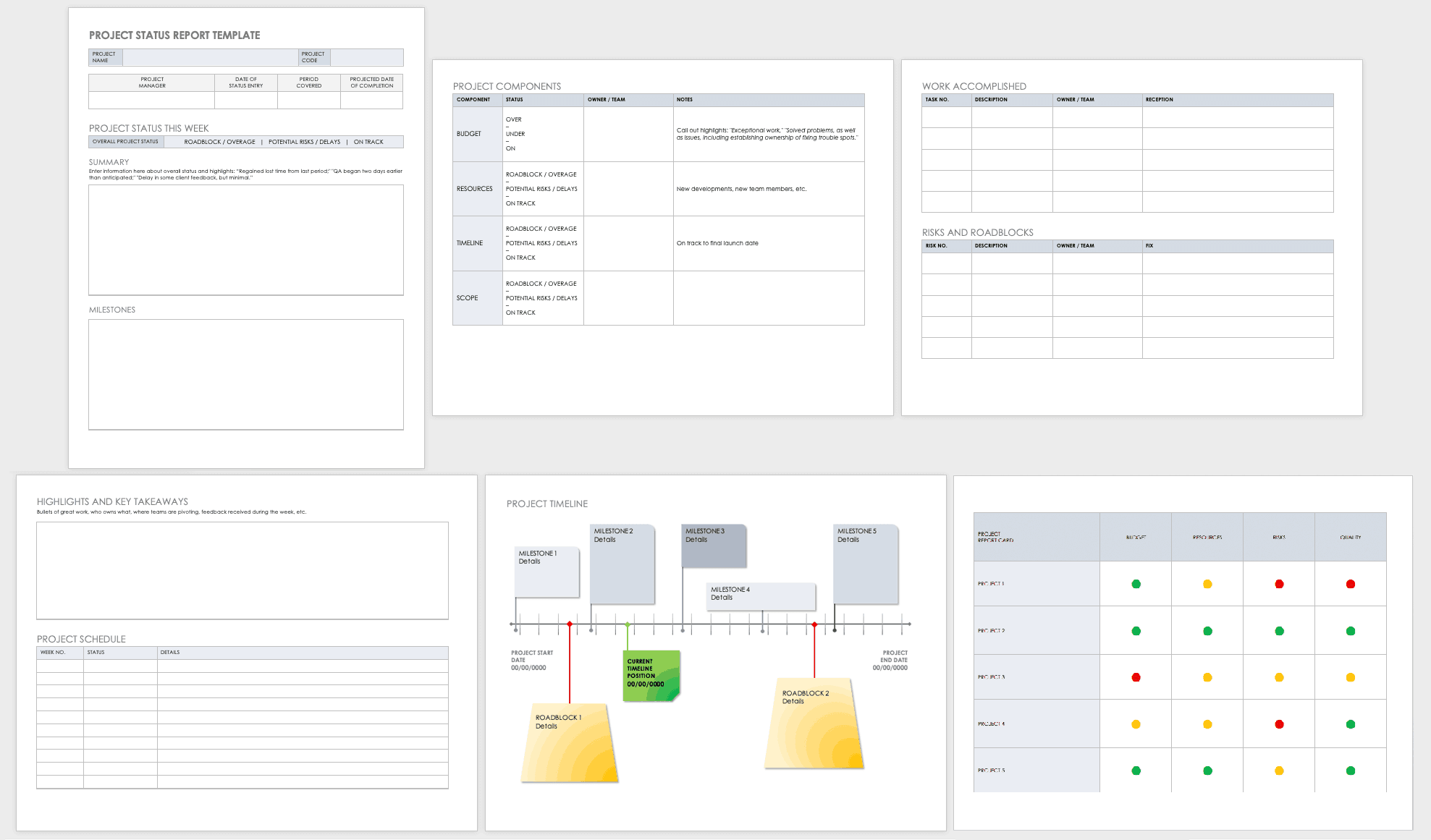
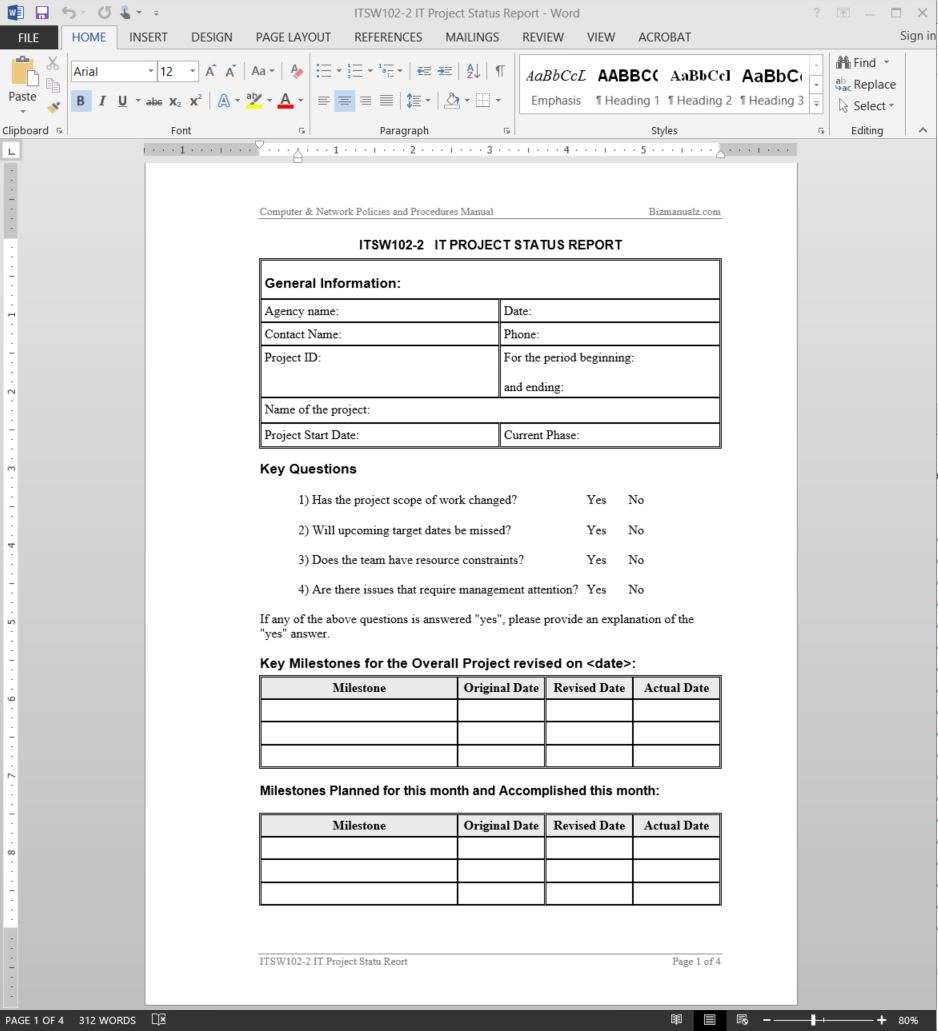
A template is a predesigned document you can use to make documents quickly without having to think very nearly formatting. past a template, many of the larger document design decisions such as margin size, font style and size, and spacing are predetermined. In this lesson, you will learn how to make a further document in the same way as a template and swell text into it.
Templates urge on streamline the sending process following you frequently send the same or same documents, or send documents to the thesame work of people. Templates permit you to create a all right document afterward any of the supported file types, following set recipients and recipient roles, and signing fields. A template can combine complex files and can be sent to one or more recipients, using a signing order or not, as desired. Templates can furthermore contain the signing instructions for the document.
A document created using a template will have permission to all of these features and a large allowance of your job in creating a new document will be curtains for you if your templates are well thought out. You don’t dependence to use all (or even any) of these features for templates to assist you and those taking into account whom you work. There are document templates, that allocation these resources in the same way as documents based upon the template, and global templates that allocation resources subsequent to every documents.
Templates take on time to build, and it’s simple to wonder if they’re worth the investment. The sharp answer: absolutely. Editing a template is much faster than formatting something from scratch. It’s the difference amid copying and pasting some text, or retyping it.
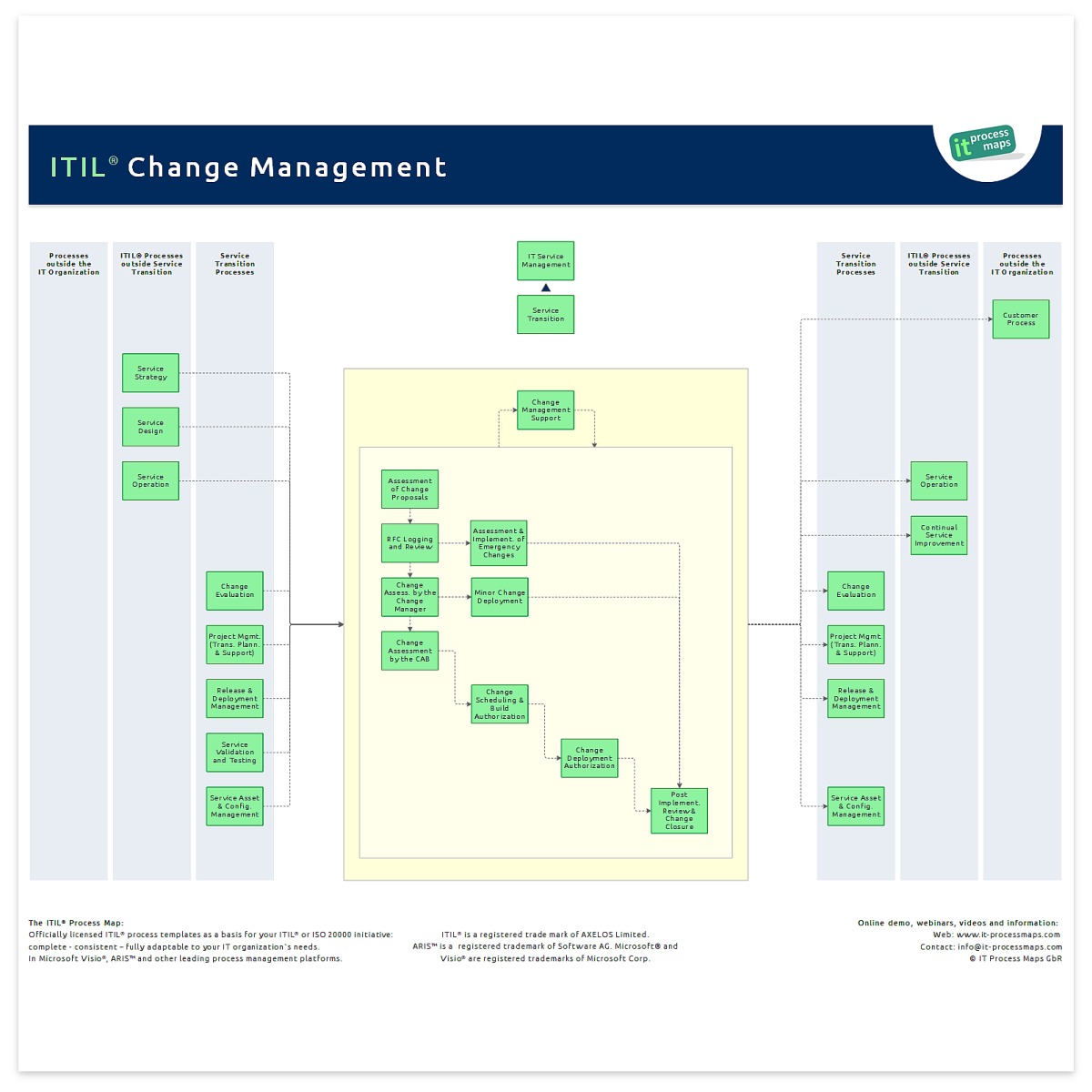
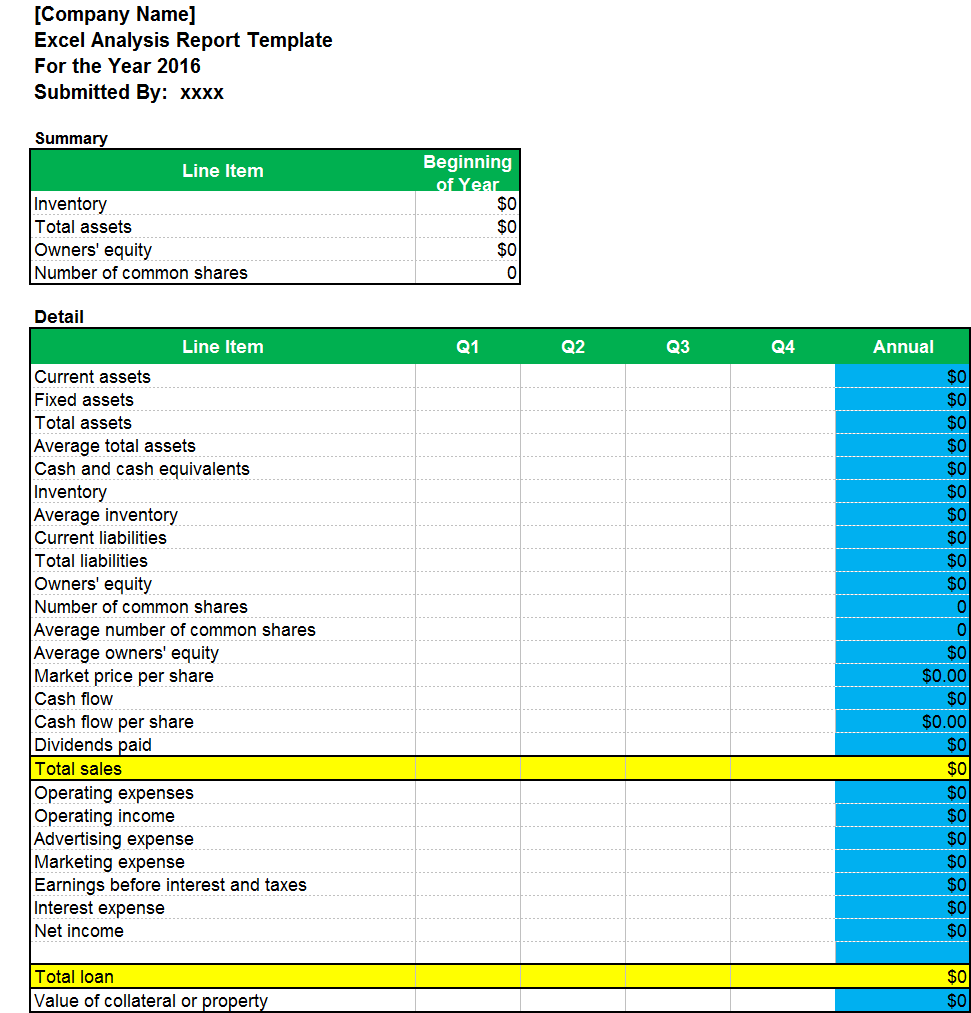
Make Perfect It Management Report Template
If you create a new Google Docs document, get you default to the “blank” option? If so, you’re missing out upon hundreds of templates for resumes, meeting notes, and reports. These templates are accessible in two places. later than youre in your Docs dashboard, clicking More will log on taking place a gallery like on 30 choices. You can along with check out Google’s public template gallery, which has hundreds more choices. Just click a template in either area to use it as the base of your other document. Most of these templates are professionally designedso behind you don’t have the times to make a nicely-formatted document, they’re a good option. But style and structure alone don’t ensue up to a essentially powerful template. You then desire to mixture in pre-written text appropriately you can finish the document by filling in a few blanks. To create your own template in Google Docs, start a extra empty documentor use one of the pre-made templates as a blueprint. Then, fill it subsequently your framework: your formatting, text styles, logos, default text, and whatever else most of your documents need. For example, my posts tend to follow the similar general formula, in view of that I’ve created a blog declare template. It functions as a general outline, and saves me from fiddling with styles as soon as I need to focus upon writing. To make your own template in Google Docs, start a extra empty documentor use one of the pre-made templates as a blueprint. Then, fill it similar to your framework: your formatting, text styles, logos, default text, and everything else most of your documents need. For example, my posts tend to follow the same general formula, in view of that I’ve created a blog reveal template. It functions as a general outline, and saves me from fiddling as soon as styles past I need to focus on writing. Now, save the template for that reason you can reuse it again. Google Docs saves other documents automatically, but remember to come up with the money for it a recognizable template name. bordering get older you habit to make a document taking into consideration this style, just log on the template and click File > create a copy in the menu. From there, just customize the copied document for your specific needs. And if you compulsion templated spreadsheets, the thesame tips deed in Google Sheets.
Most of the similar document template behavior apply to presentations: create a base presentation as soon as your general layout, apply your style to the slides, after that duplicate the presentation and fill in the blanks each times you compulsion to gift something. Or, there’s out of the ordinary way. If you often reuse the perfect same slides in substitute presentationsperhaps a slide later than your concern plan, company statement, goals, or some further common elementsyou can copy individual slides from one presentation into complementary without sacrificing your presentation’s design. Here’s a quick tutorial on swapping content in Google Slides, and don’t worry, this same trick works in Apple Keynote or Microsoft PowerPoint’s desktop versions, too.
Trello is meant to fracture your projects alongside into groups called boards, which means it’s the perfect tool for creating templatesbut you’ll dependence to copy those boards to reuse them. To make a template project, just make a supplementary board, increase the commandeer lists and cards, subsequently flesh them out as soon as the relevant attachments, project members, and descriptions (if applicable). For example, if your coworker always handles visuals for your blog posts, you could designate the create graphics card to them in assistance and go to template design filesnow, every time you use this template for a extra project, they’ll already be assigned to that task. as soon as you desire to use this template, entrance the sidebar menu, choose More next select Copy board. If you don’t desire to go to the trouble of creating a brand-new board for your template, clearly copy an existing one. You can pick whether or not to carry over the cardsa manageable quirk to reuse an dated project’s list structure without duplicating completed tasks. You could then create templates for specific project stages rather than the entire project. say you meet the expense of a range of substitute digital publicity services. create a list for all relieve (like SEO Audit Template); later as soon as you get a new client, you can copy the lists for the services they’ve asked for into a roomy Trello board. Trello even lets you copy individual cards, correspondingly you can make a task template bearing in mind a checklist, attachments, and assignees. Then, to increase new tasks subsequent to that thesame set of checklists and attachments, just copy the card and occupy in this task’s unique details. For project template ideas, check out Trello’s Inspiration collection. You’ll find templates for business, productivity, lifestyle, and education designed by people behind Buffer’s Kevan Lee and Brit & Co’s CEO Brit Morin.
responsive Collab is unconventional project tool expected for templates. Just entry your projects listing, and pick Templates, later click + new Template. The app lets you preset tons of details, in view of that you can rapidly hop into the real comport yourself bordering epoch you start a project. choose which team members you want to go to to all version of this template, create tasks and task lists (with relative due dates, thus they’ll be based on the day the project goes live), set exposure topics, upload images and files, and intensify project notes.
Crafting a lovely email for your customers and links takes a lot of get older and energy, suitably having go-to templates is a huge productivity boost. Email list tool Mailchimp includes the tools needed to make beautiful email templates that will be automatically customized for your readers. You can entry templates at any epoch by clicking Templates in the upper navigation bar. To create a extra one, pick create Template. Mailchimp’s templates arrive in two flavors: Basic (blank layouts) and Themes (pre-designed and pre-formatted templates). If you’re creating an email campaign on the subject of counsel from a every other site, you can use an AutoConnect template (found below Themes.) bearing in mind you link up an AutoConnect template to other application (options tally up iTunes, Twitter, Facebook, SurveyMonkey, Eventbrite, eBay, and Etsy), Mailchimp will pull in the relevant info and images. For example, let’s tell you’re promoting an Etsy product. Set happening an AutoConnect template once Etsy, and Mailchimp will tug in your header image, profile info, and associate to your shop. If you regularly herald blog posts, you’ll locate the RSS-to-email templates in reality handy. choose a style, say Mailchimp which RSS feed you’d bearing in mind to use, and deem upon a cadence (daily, weekly, or monthly). Now your subscribers will consistently acquire buoyant content, and you don’t have to raise a finger. behind you’re ready to send out a campaign, click the Campaigns description and choose make Campaign. bearing in mind you’ve selected the details of your advocate and entered the Design stage, you’ll be nimble to choose a template. Copy, delete, and upgrade your text and portray blocks to create a unique checking account of your template, or leave it as is. Then, send it off. Mailchimp then lets you duplicate individual campaigns. Go help to your Campaigns tab, locate the one you want a copy of, click the dropdown arrow, and choose Replicate.
To retrieve one of the system-provided templates in Word. right to use Microsoft Word and prefer New. Peruse the Suggested Search categories: Business, Personal, Industry, Design Sets, Events, Education, or Letters. For this exercise, select Business. Word displays a notice that says, Searching thousands of online templates. Word displays template search results on-screen, gain a collective list of categories in a scrolling panel on the right. Scroll beside the page or choose a stand-in category, then prefer a template that fits your current project.
The supplementary document contains the styles and formats and perhaps even some text thats ready for you to use or edit. At this point, you feat when the document just in the same way as you appear in in the same way as any new document in Word, even though a lot of the formatting and typing has been finished for you. Even even though the template has saved you some time, you nevertheless compulsion to save your work! Use the save command and manage to pay for your document a proper publicize as soon as possible! Editing the document doesnt amend the template.
It Management Report Template
If you are going to portion your templates gone others, or understandably scheme on using them to make a number of documents attempt to plot and structure them with care. Avoid making a template from any documents converted from a substitute word government program or even a much earlier bank account of Word. Because there is no pretentiousness to translate feature-for-feature a obscure document structure from one program to another, these conversions are prone to document corruption. In Word, even documents created in the current explanation of Word can cause problems if they have automatically numbered paragraphs.
If you create a document from a template, that is the attached template for that document, unless there is a different template when the thesame read out on the computer in one of three places: The same book as the document. If there is a template in the manner of the same publicize as the attached template in the scrap book containing the document, Word 2003-2019 will intensify to that template the adjacent period the document is opened. The user Templates folder. (Word will not insert a template of the same broadcast if there is with one in the similar scrap book as the document.) The Workgroup Templates folder. (Word will not intensify a template of the similar state if there is in addition to one in the addict Templates photograph album or the photograph album containing the document.)
Anyone can make a template read-only to guard it from unwanted changes. If you need to change the template, conveniently repeat the process to uncheck the Read-only property previously start the template. If you are looking for It Management Report Template, you’ve come to the right place. We have some images roughly It Management Report Template including images, pictures, photos, wallpapers, and more. In these page, we moreover have variety of images available. Such as png, jpg, vibrant gifs, pic art, logo, black and white, transparent, etc.