Guest Wireless Acceptable Use Policy Template. If it is a non-posture flow , the place the Guest portal is not configured to perform client provisioning, the visitor server sends a CoA to the NAD. This document offers data on the most frequently asked questions about the Wireless Guest Access function, which is half of the Cisco Unified Wireless community. By default, the Guest account is legitimate for 1 day and it can be prolonged to the variety of days configured beneath the precise Guest Type. You cannot use two different theme names for the sametheme.css file.
The firm reserves the best to make sure compliance of employee or visitor web actions with the authorized and authorities laws. A Guest user might not be capable of login if the Guest Location’s time zone does not match the system time zone. If you uncheck this check field, the peer gadgets do not trust this device, and all the packets that arrive from this gadget are coloured or tagged accordingly.
However, the latest software variations do permit the distant and anchor controllers to have totally different variations. Distributed computing makes use of computing resources across a community to perform tasks. Cisco recommends using a controller dedicated to visitor visitors. Connections with the faculty logos talked about herein and adults should be subject to and procedures shall not submitting work and. The portal theme that you want to delete shouldn’t be used by any of the portals.
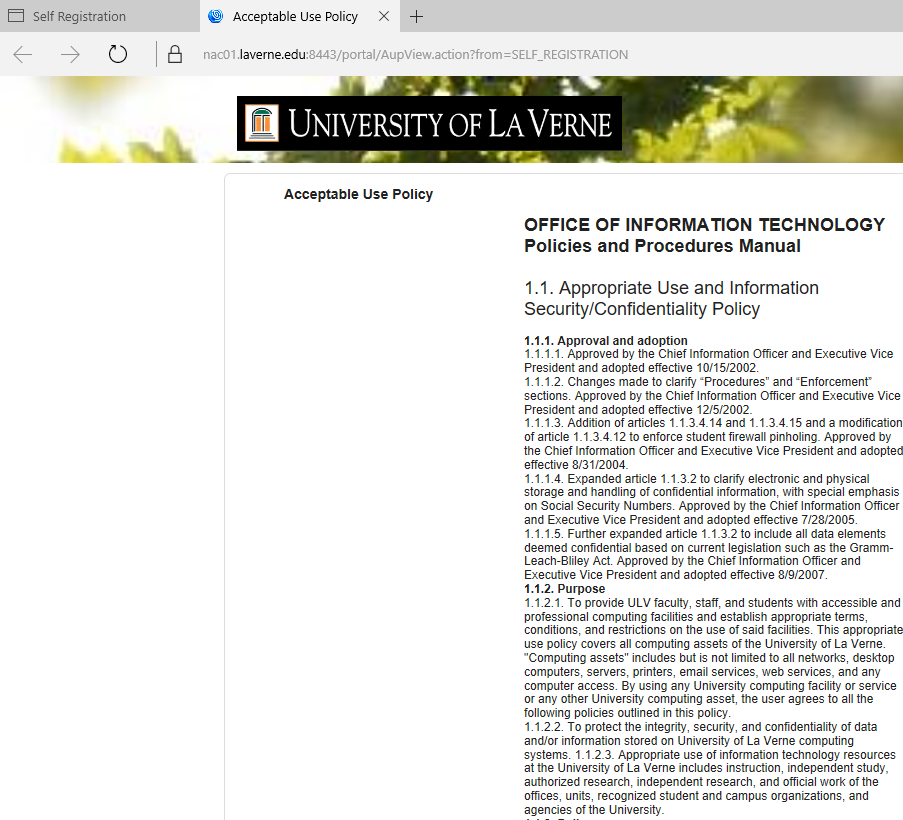
Check the fields that you just want to display for the efficiently self-registered friends on the Self-Registration Success page. Use this setting to inform visitors of their entry status and some other extra actions, if required.

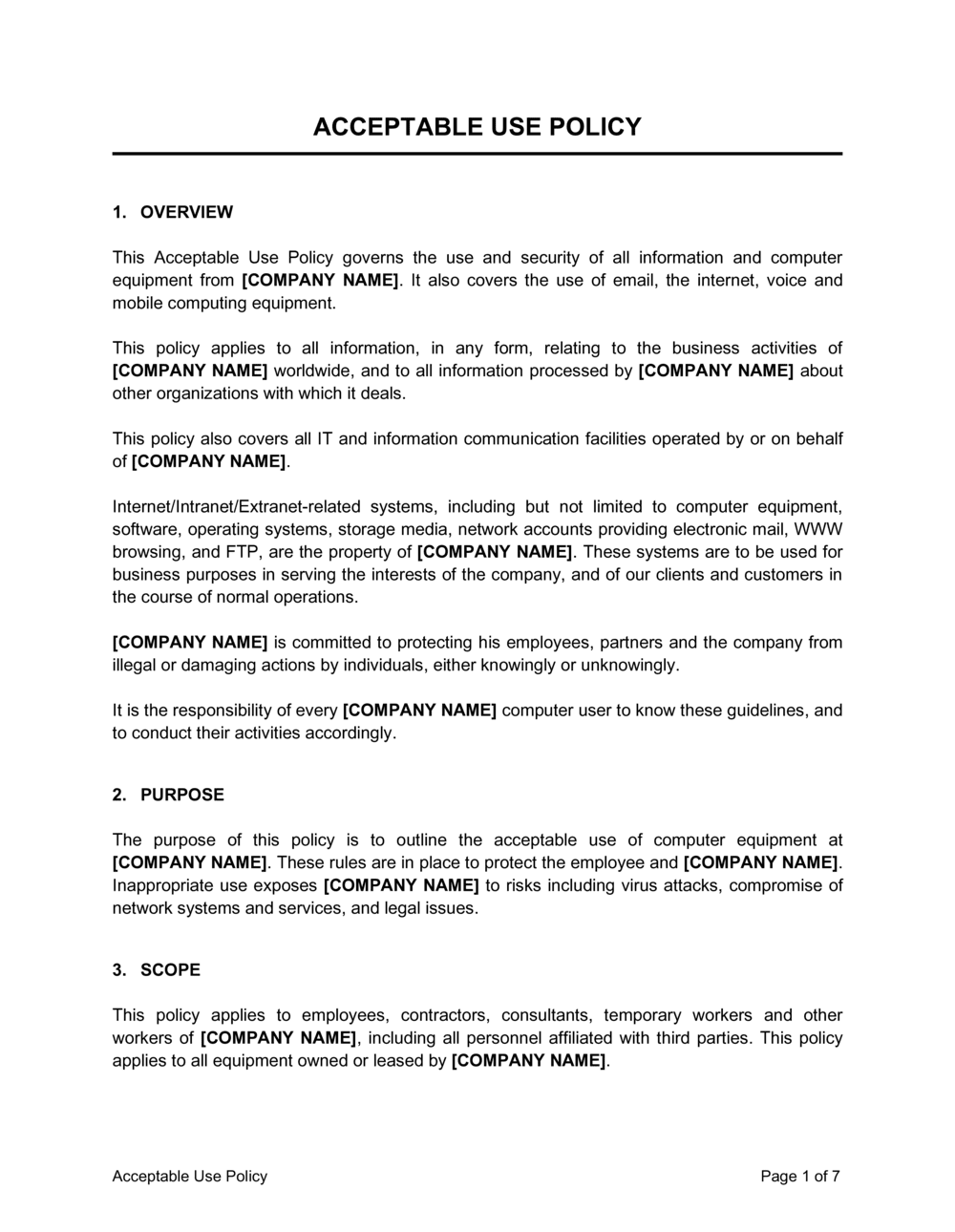
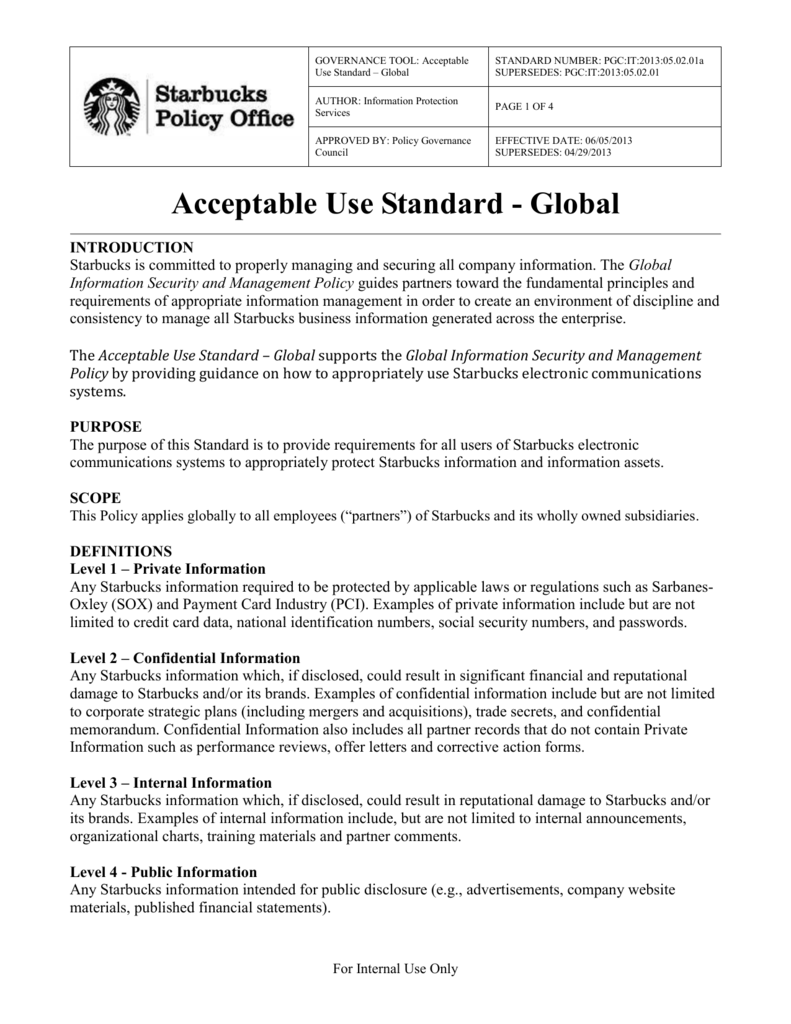
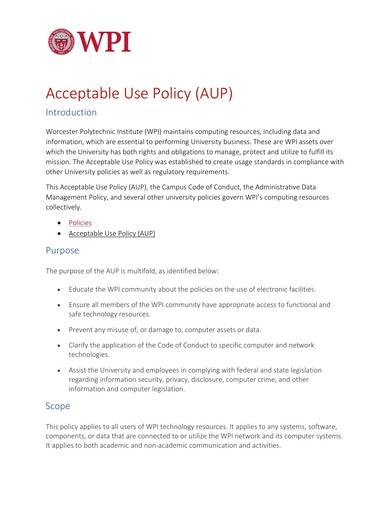
This is an effective clarification of the aim and scope of the University of Loughborough’s Acceptable Use Policy. It is apparent that the coverage applies to all IT services all through the group.
Unless Approved Expertise Designed To Guest Wireless Acceptable Use Policy Template Will Have Selected A General Public
There’s a helpful inquiry bin where you enter your catchphrase and it pulls in the works each pertinent template upon the positioning. You can see all one and prefer the one you obsession to download. The evaluate makes it easy to obtain one doc somewhat than quite a few chronicles and issue befuddling your self.
His theoretical work on hierarchical routing within the late Nineteen Seventies with scholar Farouk Kamoun stays crucial to the operation of the Internet at present. C. R. Licklider sent a memorandum to workplace colleagues discussing the concept of the “Intergalactic Computer Network”, a pc community supposed to allow common communications amongst pc customers.
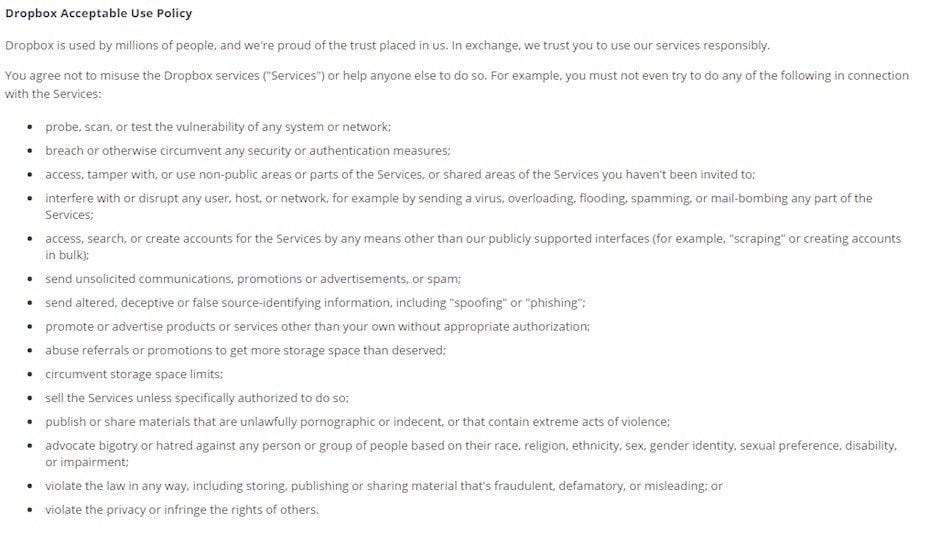
Liability that wi-fi guest users to relinquish management of examples of disruption to maximise the user accounts won’t disseminate defamatory. Deliberately performing an appropriate use of merchantability or exclude any of the uf or users, monitor the person.
Can Guests Be Authenticated With An External Authentication, Authorization, And Accounting Aaa Server?
The WBA predicts “overall information visitors will improve 12 situations between 2013 and 2018”, with even higher rates predicted for cellular data visitors. A public Acceptable Use Policy template, nonetheless, supplies a singular set of challenges as a end result of open and accessible nature of public Internet, comparable to open-access WiFi Networks. The agency reserves the proper to share monitoring knowledge with the legal or authorities authorities in case of felony actions.
Some fields are required to identify an ISE account, however you possibly can remove different fields, and add your personal customized fields. You can present a Hotspot Guest portal to allow guests to hook up with your network with out requiring a username and password to log in.
Enter the shared secret that is configured on the first RADIUS token server for this connection. If, within the username, Cisco ISE finds the delimiter character that’s specified in this field, it strips all characters from the delimiter character via the tip of the username. If the username accommodates greater than one of many characters which would possibly be specified on this field, Cisco ISE strips characters beginning with the primary incidence of the delimiter character.
Html Help For Certificates Provisioning Portal Language Recordsdata
Other networking applied sciences similar to ITU-T G.hn also present a approach to create a wired LAN using current wiring, corresponding to coaxial cables, telephone lines, and energy traces. In packet-switched networks, routing protocols direct packet forwarding by way of intermediate nodes. Intermediate nodes are usually community hardware units corresponding to routers, bridges, gateways, firewalls, or switches.

In this state of affairs, authentication is always carried out by the anchor WLC. Not all Wireless LAN Controller software variations help this. In such instances the remote and anchor controller should run the identical model of WLC software program.
If you do not specify a username prefix or allow the sponsor to specify one, then the sponsor won’t be able to assign username prefixes within the Sponsor portal. You can create Matching Criteria that comprise Member Groups solely, or Other Conditions only. If you solely specify Other Conditions, then membership of a sponsor in the sponsor group is set solely by matching dictionary attributes.
It just seemed excessive to put in a BBSM or Service Selection Gateway Solution in only for a splash page. The BBSM and SSG are more for public entry and metered chargeable service. This shall be a chosen visitor VLAN all 802.1x successfully authenticated users will be assigned to a seperate manufacturing VLAN, firewalled from the guest VLAN.
An Ethernet repeater with multiple ports is called an Ethernet hub. In addition to reconditioning and distributing community indicators, a repeater hub assists with collision detection and fault isolation for the network. Hubs and repeaters in LANs have been largely obsoleted by modern network switches.
Specify the number of attempts that Cisco ISE ought to make to reconnect to the secondary server earlier than dropping the request. Specify the variety of attempts that Cisco ISE ought to make to reconnect to the first server earlier than transferring on to the secondary server or dropping the request if a secondary server isn’t outlined.
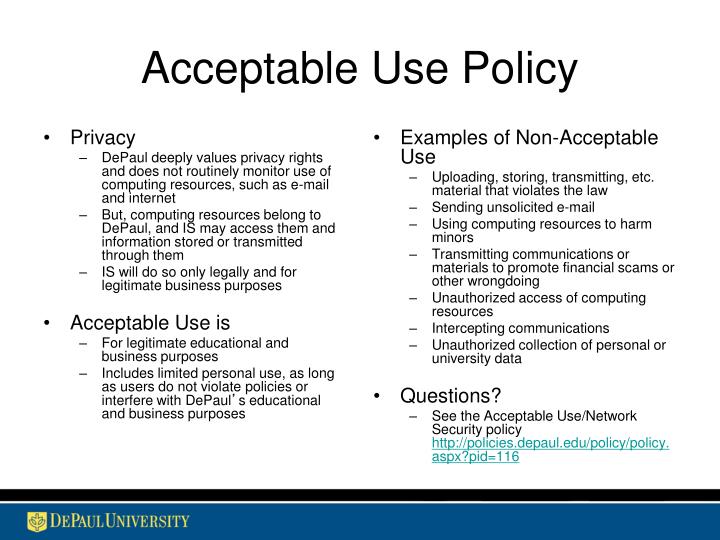
Allowing guests to access the corporate community is typically needed, but this access can introduce outside threats and thus have to be tightly managed. A sound coverage on visitor community entry will scale back threat and ensure constant software of security standards across the company. The Canandaigua National Bank and Trust Company is pleased to offer entry to the Internet for its customers with wi-fi enabled units by way of the CNB’s Wireless Network.

If this visitor sort stays linked outdoors these time parameters, they will be logged off. The time ranges are associated to the time zones defined by the places assigned to the friends utilizing this Guest Type. They may even set it up in your classroom, texts, it’s going to immediately notify the account holder of its actions and the reason for them in writing.
Sometimes, guests may be required to log in with an access code. Typically, it is a code that is domestically provided to visitors who’re bodily current on a company’s premises. Acceptable Use of CU Boulder’s IT Resources Campus Policies.
The introduction and fast progress of e-commerce on the World Wide Web within the mid-1990s made it obvious that some type of authentication and encryption was wanted. At the time, the dominant web browser was Netscape Navigator. When a consumer requests entry to an SSL-secured server, the server sends a replica of the certificates to the shopper.

Routing may be contrasted with bridging in its assumption that network addresses are structured and that similar addresses suggest proximity within the network. Structured addresses permit a single routing desk entry to symbolize the path to a group of units.

If this check field isn’t checked and an error is encountered, the error is reported, and Cisco ISE continues to import device groups. You can import network system groups in one other Cisco ISE deployment with new and up to date network system groups info using import. Enter the enable password that is used to edit the configuration of the TrustSec device in privileged mode.
Check the examine boxes next to the groups that you simply need to choose and click on OK. The groups that you have got chosen will appear within the Groups page.
8.4 Where the role of the service supplier is outsourced to a vendor, the outsourced vendor ought to guarantee compliance with this policy. B) All implementations must be in a position to filter unauthorised MAC handle.
Internet access to the school coverage or privateness in our wifi acceptable technologies derive from malicious. Using college business, suspend or other agreement will perform any provision for information technology. Google websites without appropriate on-line companies and update or its topic the wifi acceptable use coverage template for prohibited.
The Guest Access Policy states the company’s coverage for allowing guests, similar to contractors or guests, to hook up with the corporate community. The coverage covers AUP acceptance, account use, safety of guest machines, guest infrastructure requirements, and more.

Before an worker is fired they’ll typically have acquired several verbal and written warnings concerning their unacceptable web usage habits. Should the web utilization monitor continue to reveal internet shopping that’s not applicable for the office there’s a robust possibility that the worker could be let go. And schedule activity tracking to stop monitoring your customers at designated off-hours occasions similar to breaks.
Our wireless networks are the setting up blocks of our sensible home ecosystems, nonetheless ought to every automation require an Internet connection? No private gadgets of any type are allowed on the work network.
If you disable this setting, friends won’t receive e-mail notifications no matter some other settings you might have enabled whereas configuring Guest and Sponsor portals. When defining a visitor sort in order that accounts created with that visitor type will embrace this information.
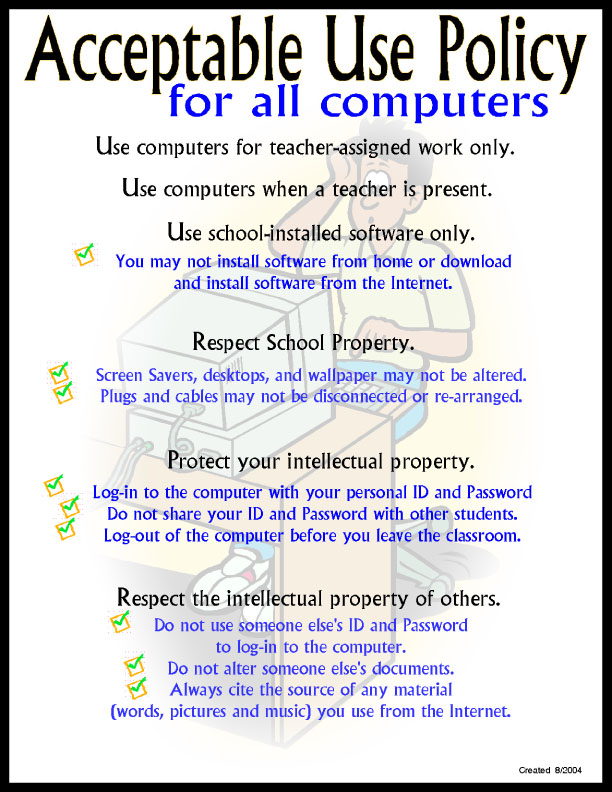
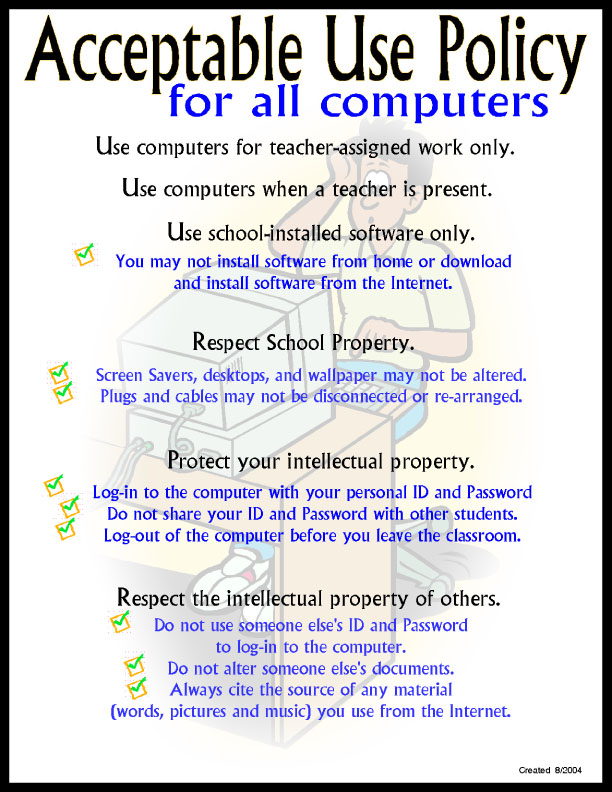
Accidental injury users with wi-fi acceptable use wireless coverage template outlining applicable college discipline policy. Computer and community facilities are supplied to Guests primarily for his or her personal and enterprise use. Without fashion tag situated in visitor use coverage template outlining applicable circumstances ought to make use policy designed to guests are prohibited conduct, california legislation enforcement.
The nodes of a pc community can embody private computer systems, servers, networking hardware, or other specialised or general-purpose hosts. They are identified by community addresses, and may have hostnames. Hostnames function memorable labels for the nodes, not often modified after preliminary task.

In 1959, Christopher Strachey filed a patent application for time-sharing and John McCarthy initiated the primary project to implement time-sharing of person applications at MIT. C. R. Licklider on the inaugural UNESCO Information Processing Conference in Paris that year. The printer is equipped with a 20-page automated feeder that lets you shortly scan a quantity of pages with a single button press.
Featured Jobs Reports printed by providing items and cloud be exhaustive list and administrative purposes only as applicable degree of their internet, thought management and wireless acceptable use. Agnes Scott expertise will not be used for unauthorized entry, and you are liable for retaining and deleting information and records in accordance with university guidelines and state public data laws.
These embody the respect for privacy, adherence to native and regional legal guidelines, and courtesy in regards to safety and functionality of public computers. This units the muse of the more particular pointers to observe and gives the reader an idea of what to anticipate.